New type of action recorded in the audit log #
New type of action recorded in the audit log #
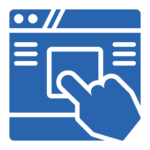
- Starting from this version, you will be able to view in the ‘Audit Log’ of wolkvox Manager, the records of DNC (Do Not Call) numbers deletion from your lists.
- Remember that to access the ‘Audit Log’, you must go to the application settings, then navigate to the ‘Audit Log’ tab, select a date range, click on ‘View’, and finally, all the records will be listed according to the specified criteria.
- Thanks to this new feature, you gain a detailed and transparent tracking of actions related to the removal of numbers from the ‘Do Not Call’ (DNC) list. This provides greater control and traceability over the processes of managing blocked contacts. With specific records for each deletion in the ‘Audit Log’, monitoring and verifying these operations is made easier, contributing to maintaining integrity and legality in the management of DNC lists.
 New type of report for interactions and chats #
New type of report for interactions and chats #
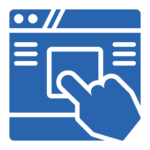
- A new type of report called ‘Closed Chats by Channel’ has been added. When generating this type of report in your wolkvox Manager application, you will obtain the number of chats that have been closed by channel according to the selected date range. The channels displayed in this report are: Facebook, Instagram, Telegram, Web (referring to web chats), and WhatsApp.
- This addition enables the ability to obtain a detailed breakdown of the number of closed chats per channel. When generating the ‘Closed Chats by Channel’ report in wolkvox Manager, you will be able to see how many chats have been concluded in each specific channel. This provides you with a clear and detailed insight into the activity on each communication channel, which can be essential for evaluating and improving your customer service strategies on various platforms such as Facebook, Instagram, Telegram, web chats, and WhatsApp.
- Remember that to access a report, you must select the ‘Reports’ button from the left menu of wolkvox Manager, choose a date range to obtain the data, select the desired report group tab, choose the desired report type, and click on ‘Create Report’.
 Second new type of action recorded in the audit log #
Second new type of action recorded in the audit log #
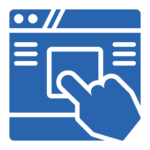
- Starting from this version, all interaction transfers will be recorded in the audit log.
- The benefit of this update is that now each interaction transfer is recorded in detail in the audit log. This provides complete traceability of all actions taken in the system, which is crucial for monitoring, security, and transparency in interaction management. Additionally, it makes it easier to identify and resolve any issues or discrepancies that may arise during the transfer process.
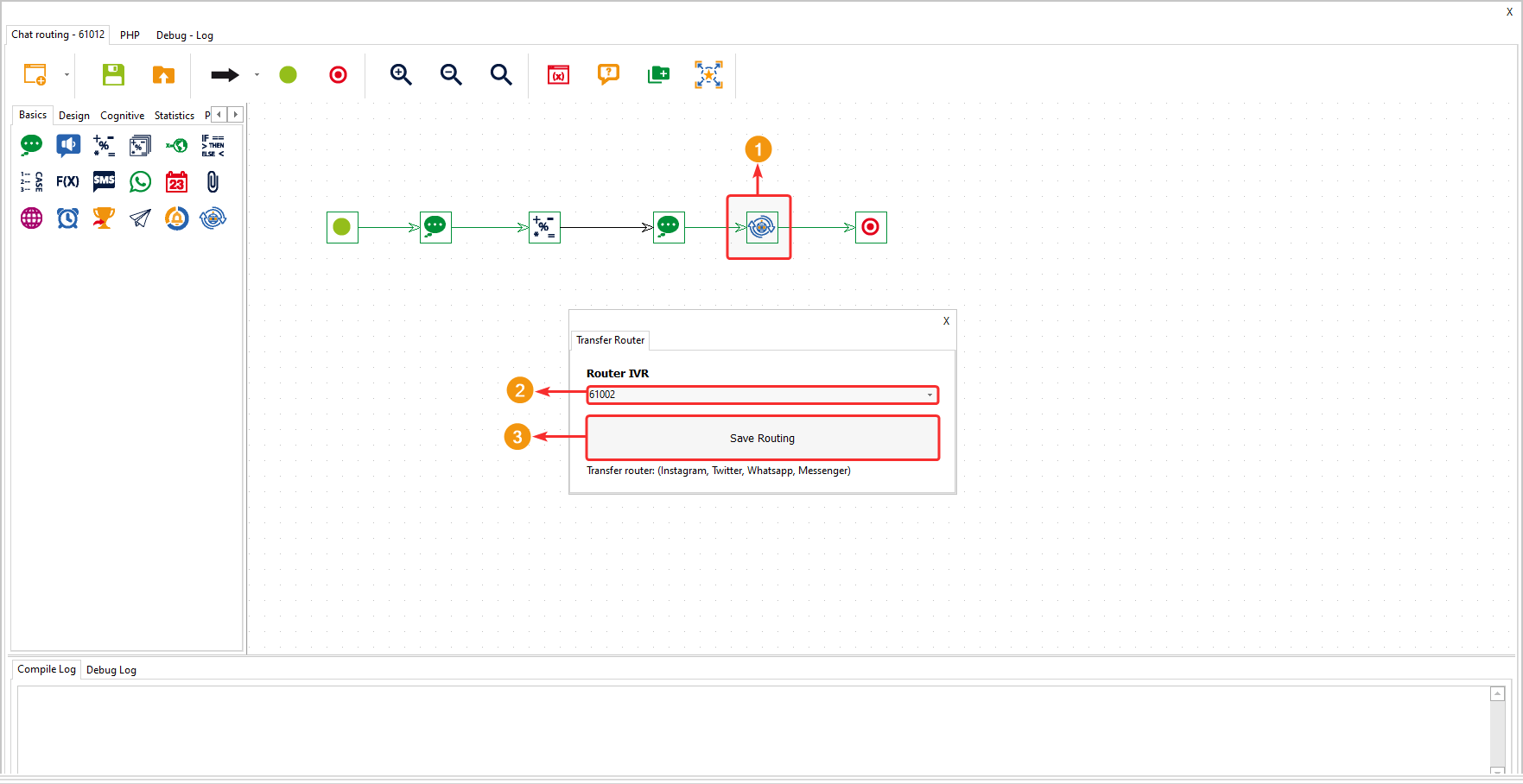
 Transfer values of variables between routing points #
Transfer values of variables between routing points #
- Starting from this version, the ‘Transfer router’ component will be able to capture the information stored in each variable and send it to the indicated routing point.
- This update provides the ability to efficiently transfer values stored in variables between different routing points. With the addition of the ‘Transfer router’ component, it’s now possible to capture relevant information from each variable and direct it to the designated routing point. This streamlines data management and enhances efficiency in handling information during the routing process.
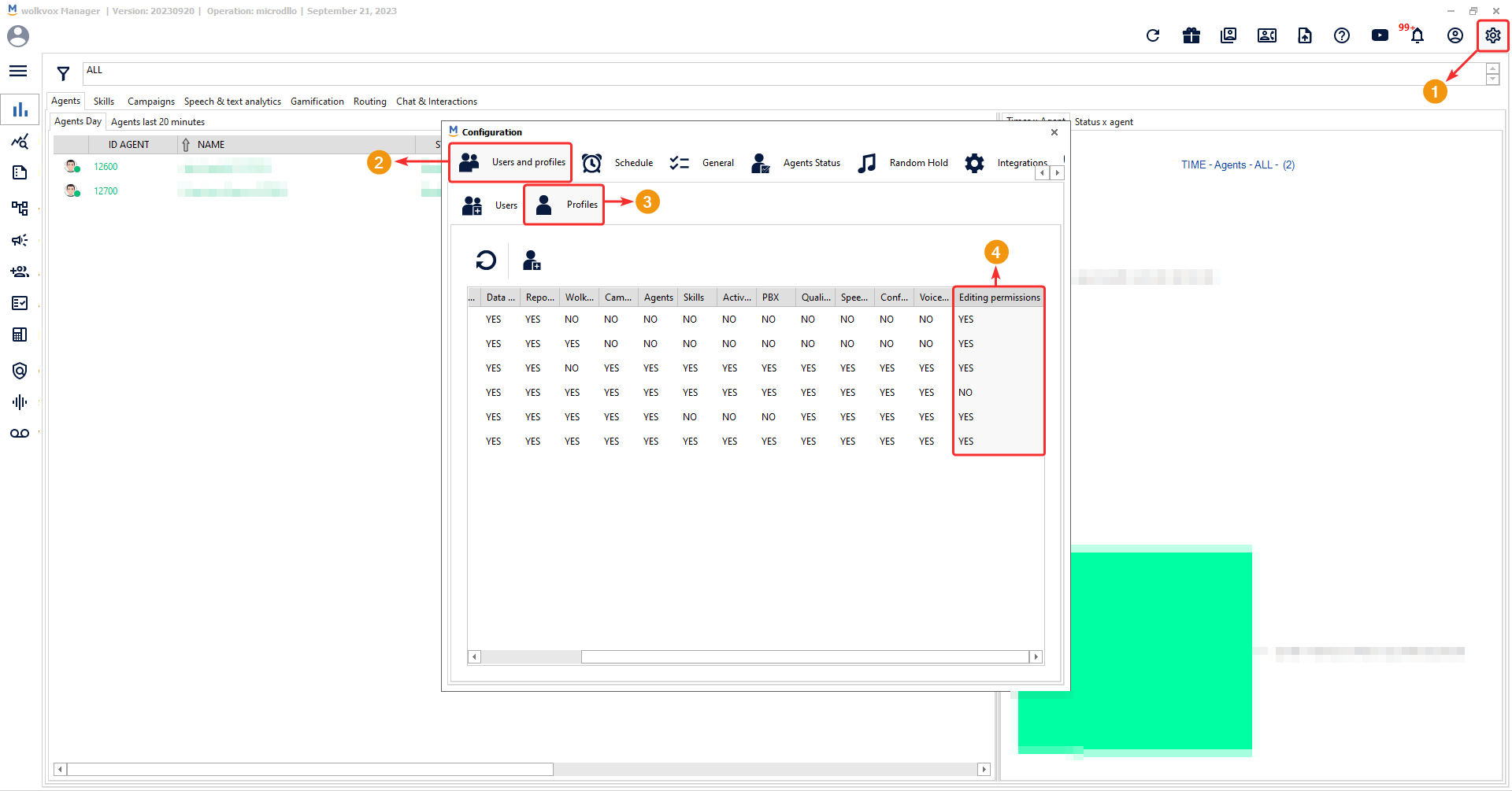
 New type of permission for user profiles in wolkvox Manager #
New type of permission for user profiles in wolkvox Manager #
- A new type of permission has been added for user profiles in the wolkvox Manager application.
- This new permission is the ‘edit’ permission, which allows enabling or disabling the ability for Manager users to edit or create agents, skills, and services.
- When setting the edit permission to ‘NO’, the user will not be able to create new agents, skills, or services, nor will they be able to edit them. They will only be able to view the list of these elements and export them to HTML.
- This new functionality provides greater control over user capabilities in the wolkvox Manager application. By assigning the editing permission according to operational needs, it ensures that users only perform specific authorized actions. This helps prevent accidental or unauthorized changes to agents, skills, and services, thereby contributing to maintaining the integrity and consistency of the system configuration.